Most Recent Fortinet FCSS_SASE_AD-23 Exam Dumps
Prepare for the Fortinet FCSS - FortiSASE 23 Administrator exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Fortinet FCSS_SASE_AD-23 exam and achieve success.
The questions for FCSS_SASE_AD-23 were last updated on Mar 30, 2025.
- Viewing page 1 out of 6 pages.
- Viewing questions 1-5 out of 30 questions
An organization needs to resolve internal hostnames using its internal rather than public DNS servers for remotely connected endpoints. Which two components must be configured on FortiSASE to achieve this? (Choose two.)
To resolve internal hostnames using internal DNS servers for remotely connected endpoints, the following two components must be configured on FortiSASE:
Split DNS Rules:
Split DNS allows the configuration of specific DNS queries to be directed to internal DNS servers instead of public DNS servers.
This ensures that internal hostnames are resolved using the organization's internal DNS infrastructure, maintaining privacy and accuracy for internal network resources.
Split Tunneling Destinations:
Split tunneling allows specific traffic (such as DNS queries for internal domains) to be routed through the VPN tunnel while other traffic is sent directly to the internet.
By configuring split tunneling destinations, you can ensure that DNS queries for internal hostnames are directed through the VPN to the internal DNS servers.
FortiOS 7.2 Administration Guide: Provides details on configuring split DNS and split tunneling for VPN clients.
FortiSASE 23.2 Documentation: Explains the implementation and configuration of split DNS and split tunneling for securely resolving internal hostnames.
Which two components are part of onboarding a secure web gateway (SWG) endpoint? (Choose two)
Onboarding a Secure Web Gateway (SWG) endpoint involves several components to ensure secure and effective integration with FortiSASE. Two key components are the FortiSASE CA certificate and the proxy auto-configuration (PAC) file.
FortiSASE CA Certificate:
The FortiSASE CA certificate is essential for establishing trust between the endpoint and the FortiSASE infrastructure.
It ensures that the endpoint can securely communicate with FortiSASE services and inspect SSL/TLS traffic.
Proxy Auto-Configuration (PAC) File:
The PAC file is used to configure the endpoint to direct web traffic through the FortiSASE proxy.
It provides instructions on how to route traffic, ensuring that all web requests are properly inspected and filtered by FortiSASE.
FortiOS 7.2 Administration Guide: Details on onboarding endpoints and configuring SWG.
FortiSASE 23.2 Documentation: Explains the components required for integrating endpoints with FortiSASE and the process for deploying the CA certificate and PAC file.
You are designing a new network for Company X and one of the new cybersecurity policy requirements is that all remote user endpoints must always be connected and protected Which FortiSASE component facilitates this always-on security measure?
The unified FortiClient component of FortiSASE facilitates the always-on security measure required for ensuring that all remote user endpoints are always connected and protected.
Unified FortiClient:
FortiClient is a comprehensive endpoint security solution that integrates with FortiSASE to provide continuous protection for remote user endpoints.
It ensures that endpoints are always connected to the FortiSASE infrastructure, even when users are off the corporate network.
Always-On Security:
The unified FortiClient maintains a persistent connection to FortiSASE, enforcing security policies and protecting endpoints against threats at all times.
This ensures compliance with the cybersecurity policy requiring constant connectivity and protection for remote users.
FortiOS 7.2 Administration Guide: Provides information on configuring and managing FortiClient for endpoint security.
FortiSASE 23.2 Documentation: Explains how FortiClient integrates with FortiSASE to deliver always-on security for remote endpoints.
Refer to the exhibits.
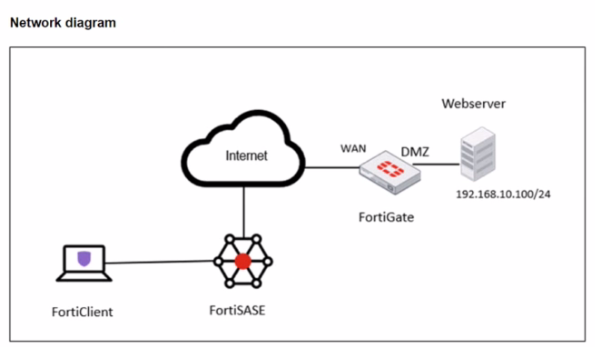
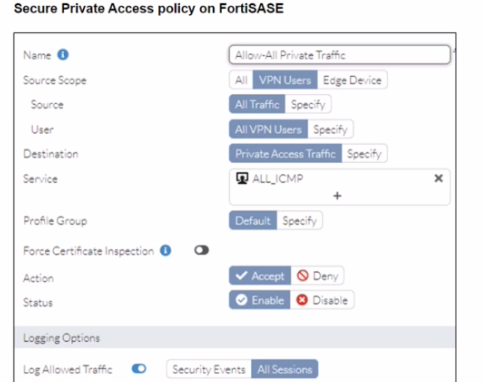
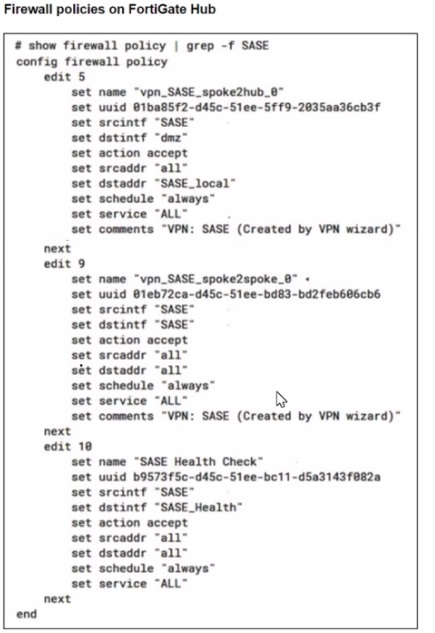
A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub. The tunnel is up to the FortiGale hub. However, the administrator is not able to ping the webserver hosted behind the FortiGate hub.
Based on the output, what is the reason for the ping failures?
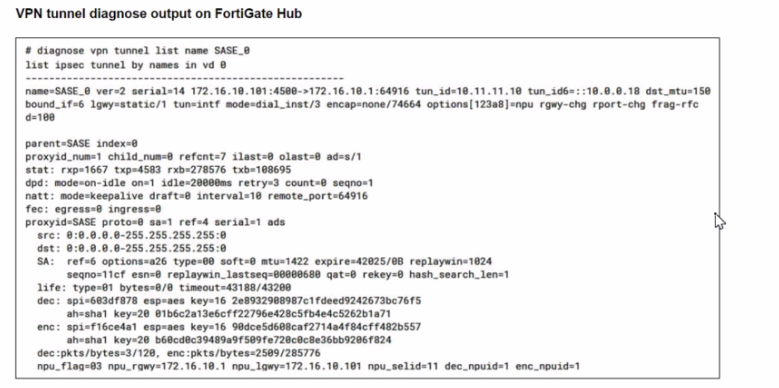
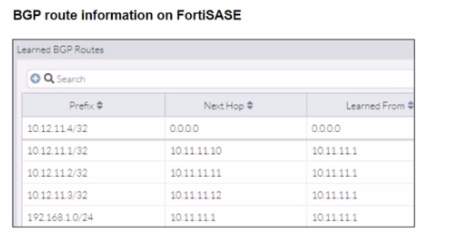
The reason for the ping failures is due to the quick mode selectors restricting the subnet. Quick mode selectors define the IP ranges and protocols that are allowed through the VPN tunnel, and if they are not configured correctly, traffic to certain subnets can be blocked.
Quick Mode Selectors:
Quick mode selectors specify the source and destination subnets that are allowed to communicate through the VPN tunnel.
If the selectors do not include the subnet of the webserver (192.168.10.0/24), then the traffic will be restricted, and the ping will fail.
Diagnostic Output:
The diagnostic output shows the VPN configuration details, but it is important to check the quick mode selectors to ensure that the necessary subnets are included.
If the quick mode selectors are too restrictive, they will prevent traffic to and from the specified subnets.
Configuration Check:
Verify the quick mode selectors on both the FortiSASE and FortiGate hub to ensure they match and include the subnet of the webserver.
Adjust the selectors to allow the necessary subnets for successful communication.
FortiOS 7.2 Administration Guide: Provides detailed information on configuring VPN tunnels and quick mode selectors.
FortiSASE 23.2 Documentation: Explains how to set up and manage VPN tunnels, including the configuration of quick mode selectors.
To complete their day-to-day operations, remote users require access to a TCP-based application that is hosted on a private web server. Which FortiSASE deployment use case provides the most efficient and secure method for meeting the remote users' requirements?
Zero Trust Network Access (ZTNA) private access provides the most efficient and secure method for remote users to access a TCP-based application hosted on a private web server. ZTNA ensures that only authenticated and authorized users can access specific applications based on predefined policies, enhancing security and access control.
Zero Trust Network Access (ZTNA):
ZTNA operates on the principle of 'never trust, always verify,' continuously verifying user identity and device security posture before granting access.
It provides secure and granular access to specific applications, ensuring that remote users can securely access the TCP-based application hosted on the private web server.
Secure and Efficient Access:
ZTNA private access allows remote users to connect directly to the application without needing a full VPN tunnel, reducing latency and improving performance.
It ensures that only authorized users can access the application, providing robust security controls.
FortiOS 7.2 Administration Guide: Provides detailed information on ZTNA and its deployment use cases.
FortiSASE 23.2 Documentation: Explains how ZTNA can be used to provide secure access to private applications for remote users.
Unlock All Questions for Fortinet FCSS_SASE_AD-23 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 30 Questions & Answers