Most Recent HashiCorp Vault-Associate Exam Questions & Answers
Prepare for the HashiCorp Certified: Vault Associate (002) exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the HashiCorp Vault-Associate exam and achieve success.
The questions for Vault-Associate were last updated on Jan 18, 2025.
- Viewing page 1 out of 11 pages.
- Viewing questions 1-5 out of 57 questions
When creating a policy, an error was thrown:
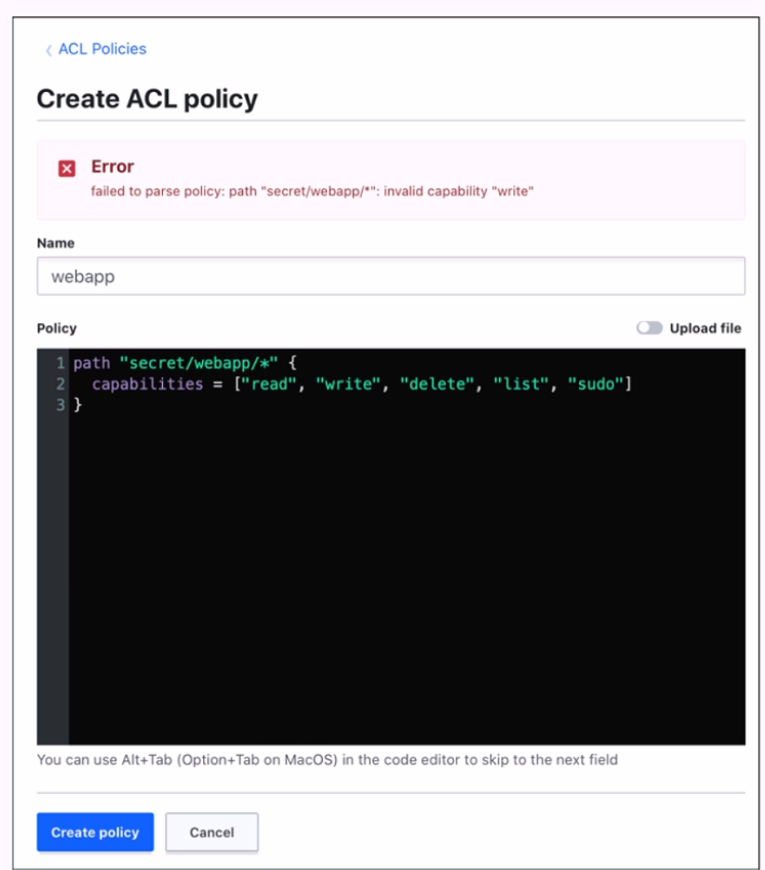
Which statement describes the fix for this issue?
The error was thrown because the policy code contains an invalid capability, ''write''. The valid capabilities for a policy are ''create'', ''read'', ''update'', ''delete'', ''list'', and ''sudo''. The ''write'' capability is not recognized by Vault and should be replaced with ''create'', which allows creating new secrets or overwriting existing ones. The other statements are not correct, because the wildcard (*) and the sudo capability are both valid in a policy. The wildcard matches any number of characters within a path segment, and the sudo capability allows performing certain operations that require root privileges.
[Policy Syntax | Vault | HashiCorp Developer]
[Policy Syntax | Vault | HashiCorp Developer]
A web application uses Vault's transit secrets engine to encrypt data in-transit. If an attacker intercepts the data in transit which of the following statements are true? Choose two correct answers.
A web application that uses Vault's transit secrets engine to encrypt data in-transit can benefit from the following security features:
Even if the attacker was able to access the raw data, they would only have encrypted bits (TLS in transit). This means that the attacker would need to obtain the encryption key from Vault in order to decrypt the data, which is protected by Vault's authentication and authorization mechanisms. The transit secrets engine does not store the data sent to it, so the attacker cannot access the data from Vault either.
The keys can be rotated and min_decryption_version moved forward to ensure this data cannot be decrypted. This means that the web application can periodically change the encryption key used to encrypt the data, and set a minimum decryption version for the key, which prevents older versions of the key from being used to decrypt the data. This way, even if the attacker somehow obtained an old version of the key, they would not be able to decrypt the data that was encrypted with a newer version of the key.
The other statements are not true, because:
You cannot rotate the encryption key so that the attacker won't be able to decrypt the data. Rotating the key alone does not prevent the attacker from decrypting the data, as they may still have access to the old version of the key that was used to encrypt the data. You need to also move the min_decryption_version forward to invalidate the old version of the key.
Which of the following statements are true about Vault policies? Choose two correct answers.
Vault does not need to be restarted in order for a policy change to take effect, as policies are stored and evaluated in memory. Any change to a policy is immediately reflected in the system, and any token or role that has that policy attached will be affected by the change.
Unlock All Questions for HashiCorp Vault-Associate Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 57 Questions & Answers